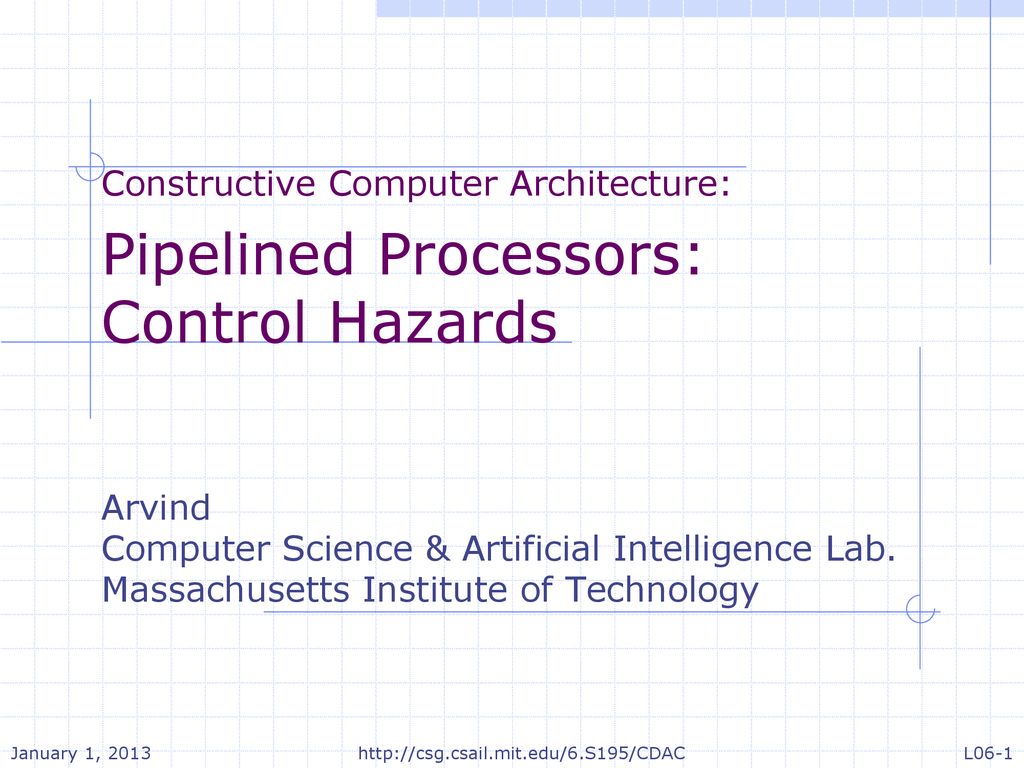
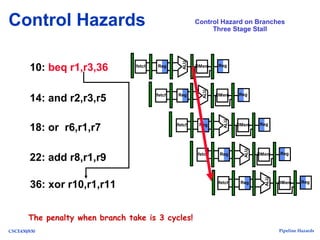
Last update images today Hazards In Computer Architecture
 Vini Jr. 'almost Perfect' As Brazil Get Back On Track
Vini Jr. 'almost Perfect' As Brazil Get Back On Track
Former USC defensive back Ceyair Wright has committed to transfer to Nebraska, he told ESPN.
Wright started 15 games for the Trojans the past two seasons and has played in 23 career games, with six pass breakups and one interception. He also has gained notice for his acting career.
Wright joins a team that finished in the top 15 in total defense and scoring defense last year under coordinator Tony White. The Cornhuskers return seven defensive starters and 10 on offense, which has led to high expectations in 2024 after the team went 5-7 in Matt Rhule's debut season at Nebraska.
The culture of Nebraska appealed to Wright, who told ESPN: "The thing that caught my attention was how much all the coaches poured into me. Everyone was invested in me to elevate me as a person and player."
Wright is a former top 110 recruit in ESPN's rankings from the class of 2021, and he will have two seasons of eligibility remaining at Nebraska after redshirting his 2021 season.
He started 11 games in 2022. Wright also has thrived as an actor and model, appearing in television shows ranging from "2 Broke Girls" to "Training Day." He gained the most renown for playing the son of LeBron James in the movie "Space Jam: A New Legacy," released in 2021.